Implement SAML SSO using Okta
Configure a connection to Okta via SAML.
Step 1: Request SSO Setup
Start by reaching out to your Customer Success Manager to ensure your current plan allows SSO setup. Then loop in the Support Team ([email protected]) and ask them to kickstart the process.
Step 2: Configure the connection between your Identity Provider (IdP) and Synthesia’s SSO service provider
- After the support team sends you the WorkOS setup link, please click on it and follow the Admin Portal instructions
- You will see a list of the IdP providers available. Choose the one you need and follow the corresponding step-by-step guidelines on how to configure the IdP settings.
Once done, you will be able to test your SSO integration with that identity provider.
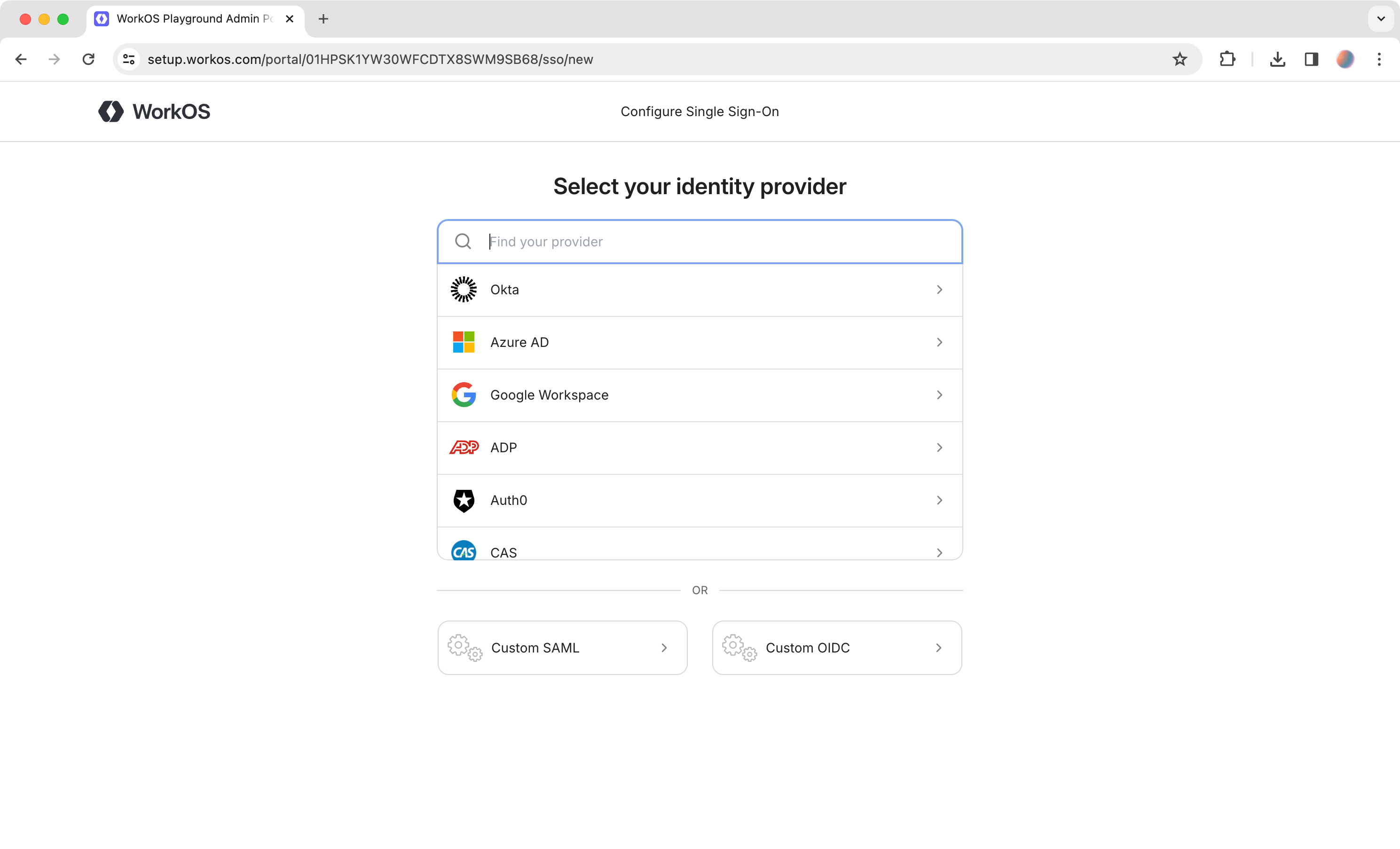
Configure Single Sign-On - WorkOS
Step 3: Create a SAML Integration
- Sign in to the Okta admin console.
- In the left navigation menu, expand the Application section and select the
Applicationstab.
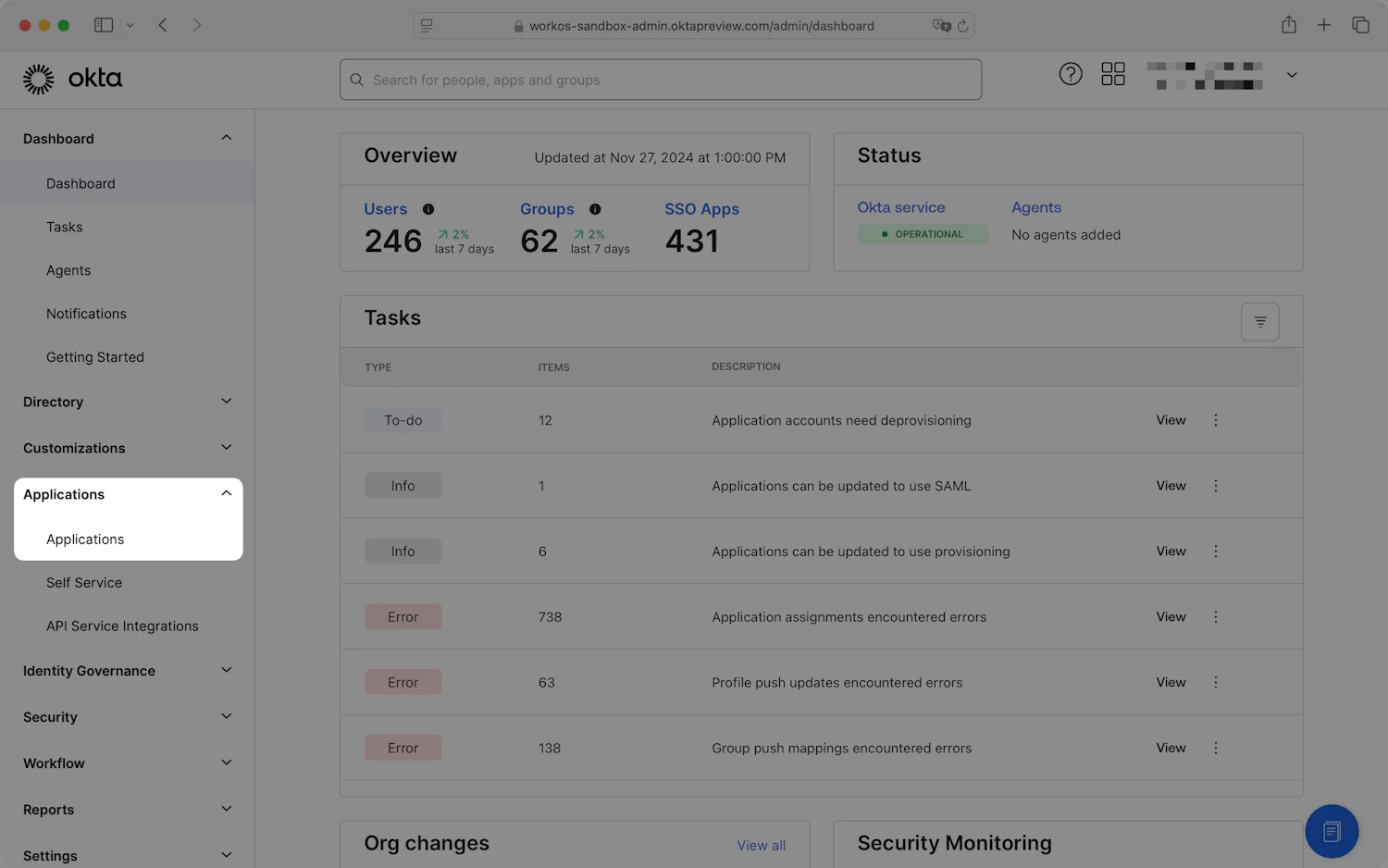
Dashboard - Okta admin console
- Click
Create App Integration.
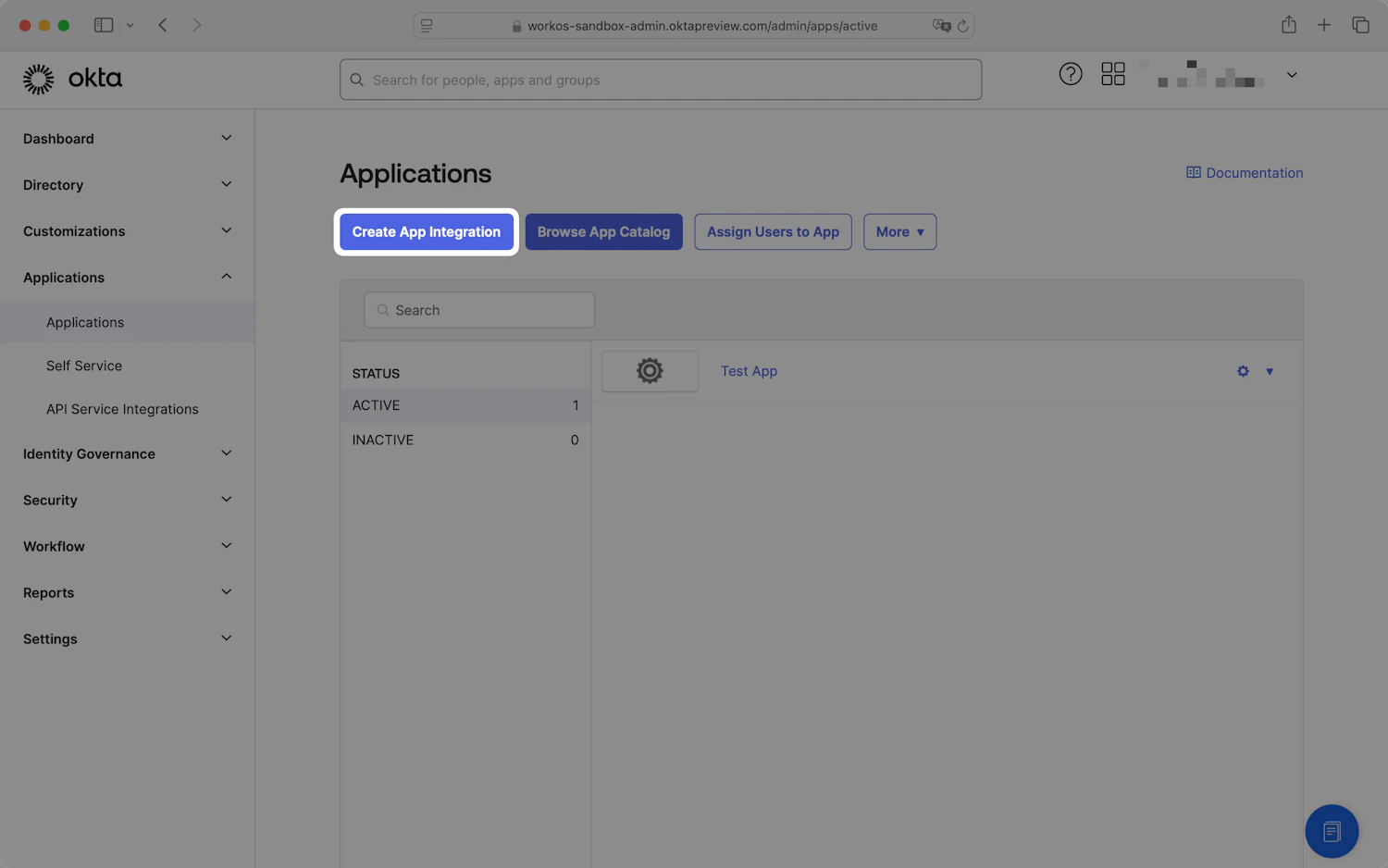
Applications - Okta admin console
- In the Create a new app integration dialog, select
SAML 2.0and clickNext.
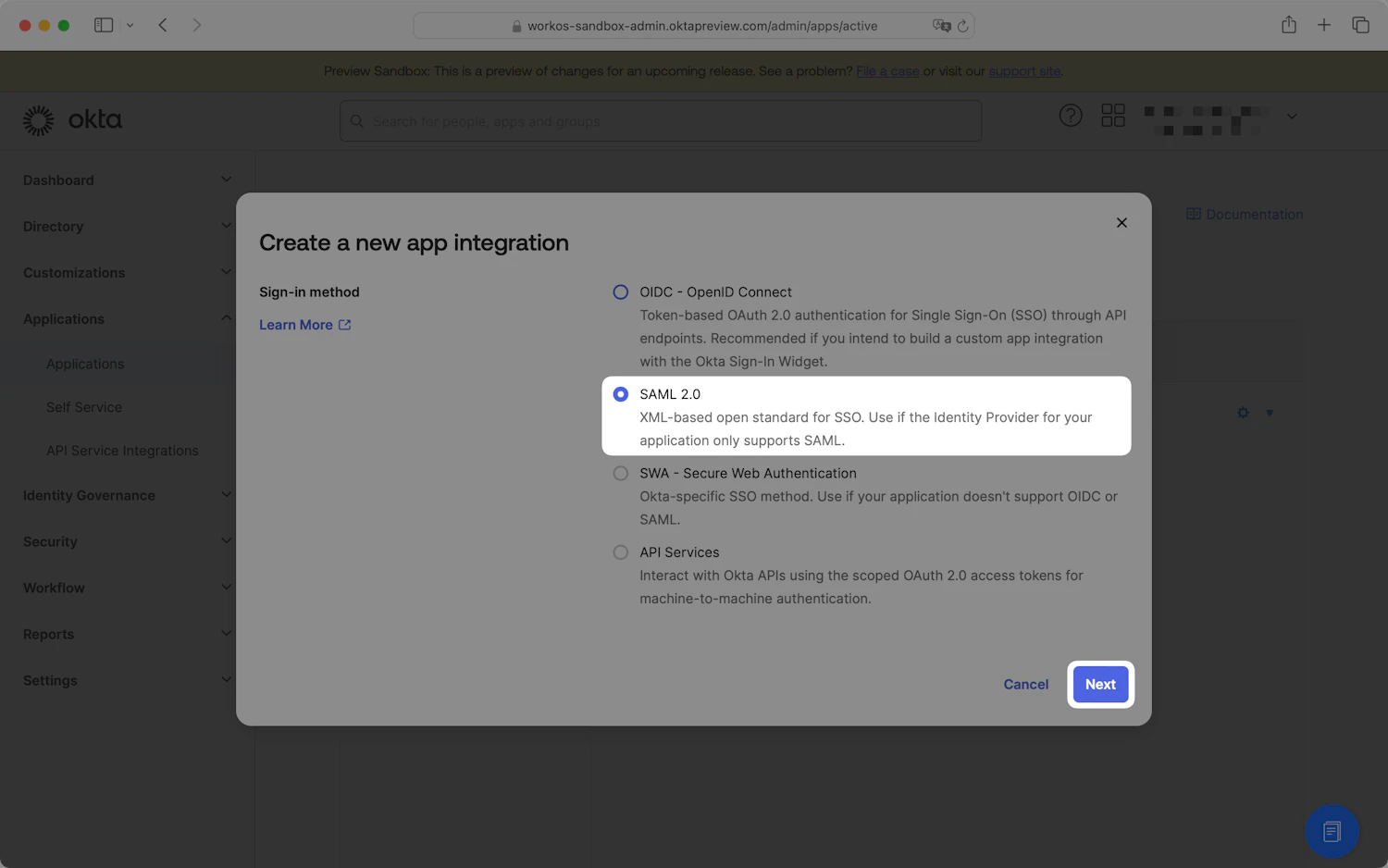
Create a new app integration dialog
- The Create SAML Integration wizard will open. For the General Settings step, enter an appropriate app name, such as "Synthesia". Optionally, you can upload an app logo. Click
Next.
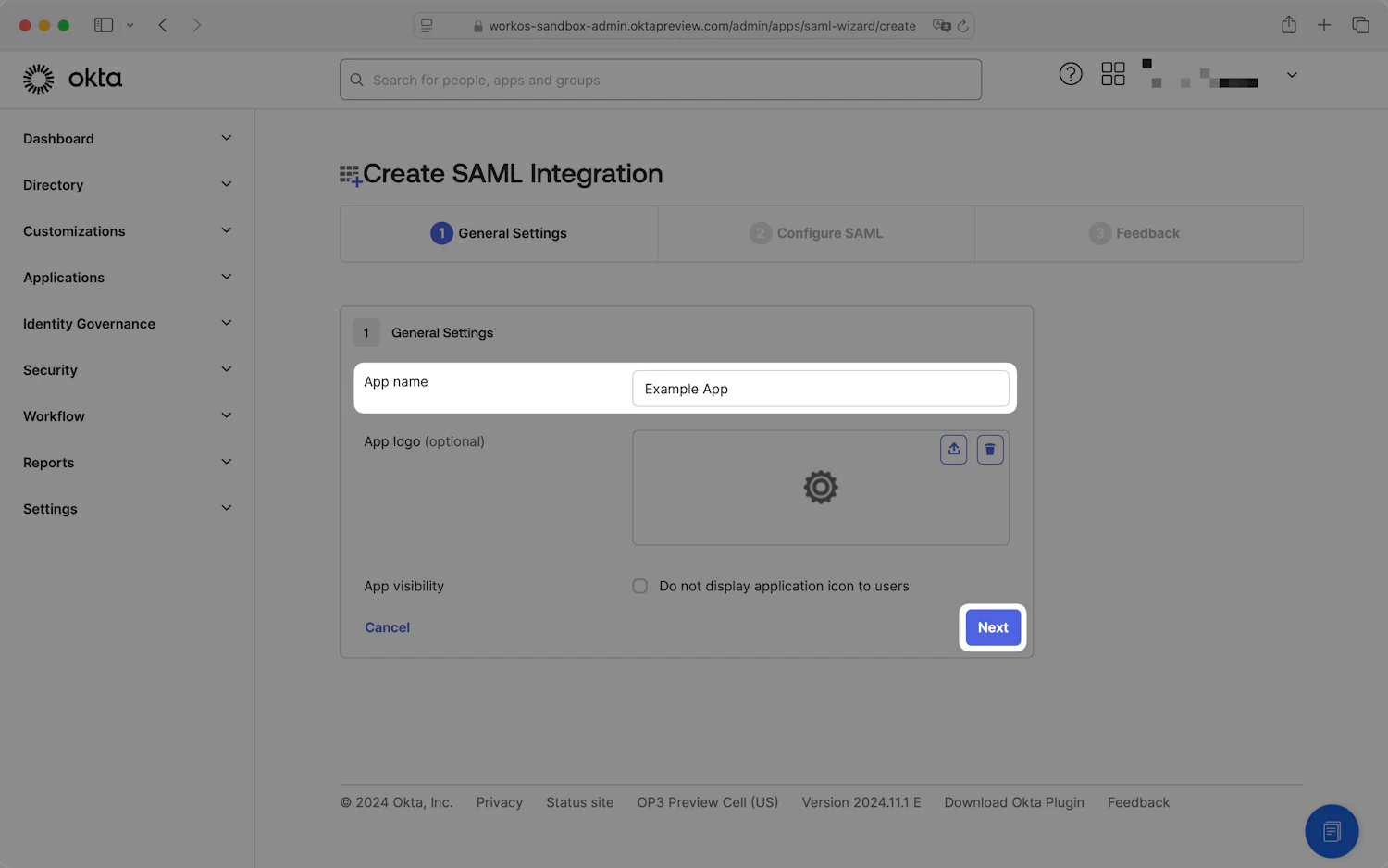
Create SAML Integration wizard
- On the Configure SAML step, locate the Single Sign-On URL and Audience URI (SP Entity ID) fields.
- Copy the values from the WorkOS setup guide you received and paste them into their respective fields in the Okta admin console.
| Single sign-on URL | Audience URI |
|---|---|
https://studio.auth.synthesia.io/saml2/idpresponse | urn:amazon:cognito:sp:eu-west-1_7hEawdalF |
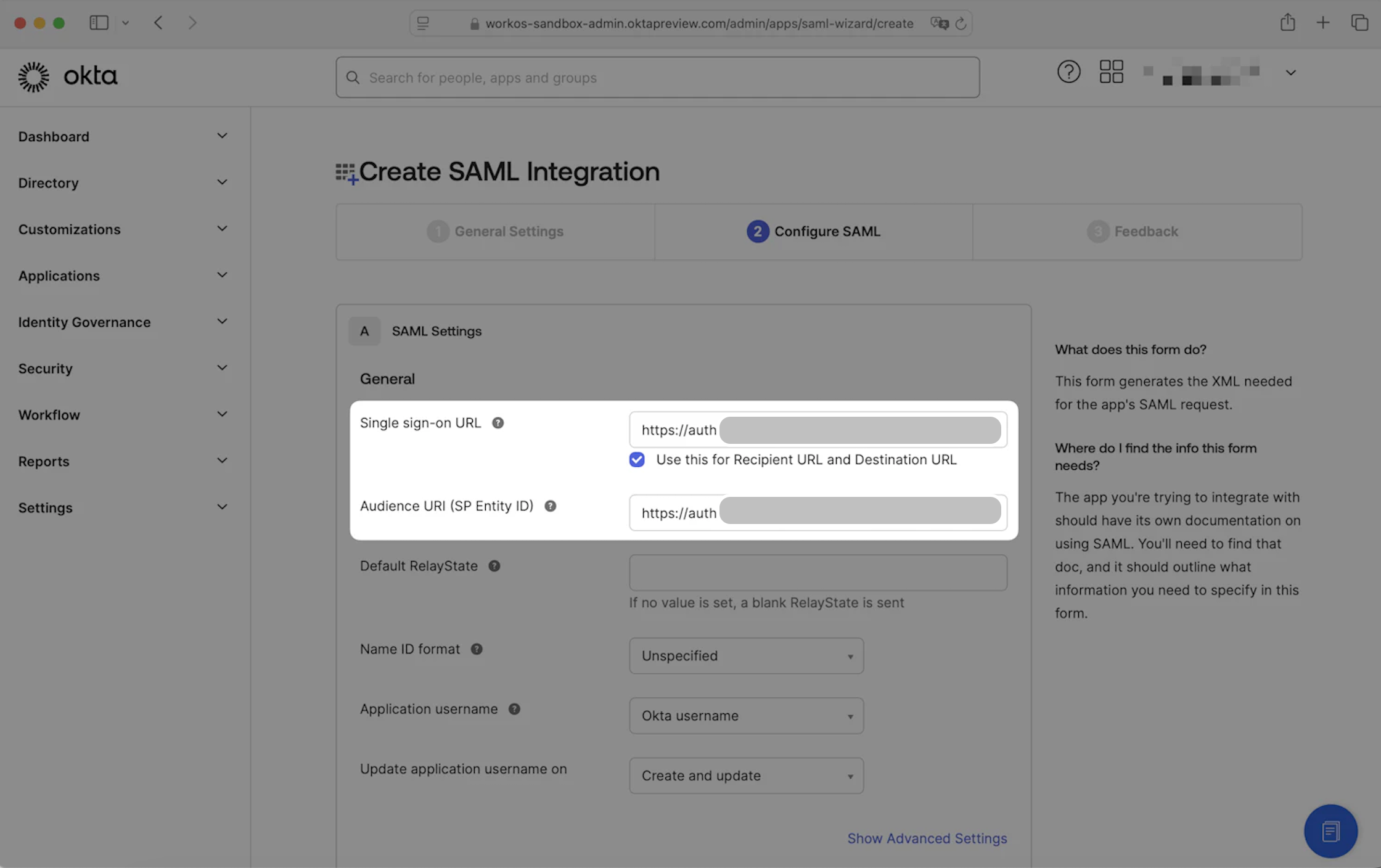
Single sign-on URL and Audience URI (SP Entity ID) fields - Create SAML Integration wizard
- Scroll down to the bottom of the page, then click
Next.
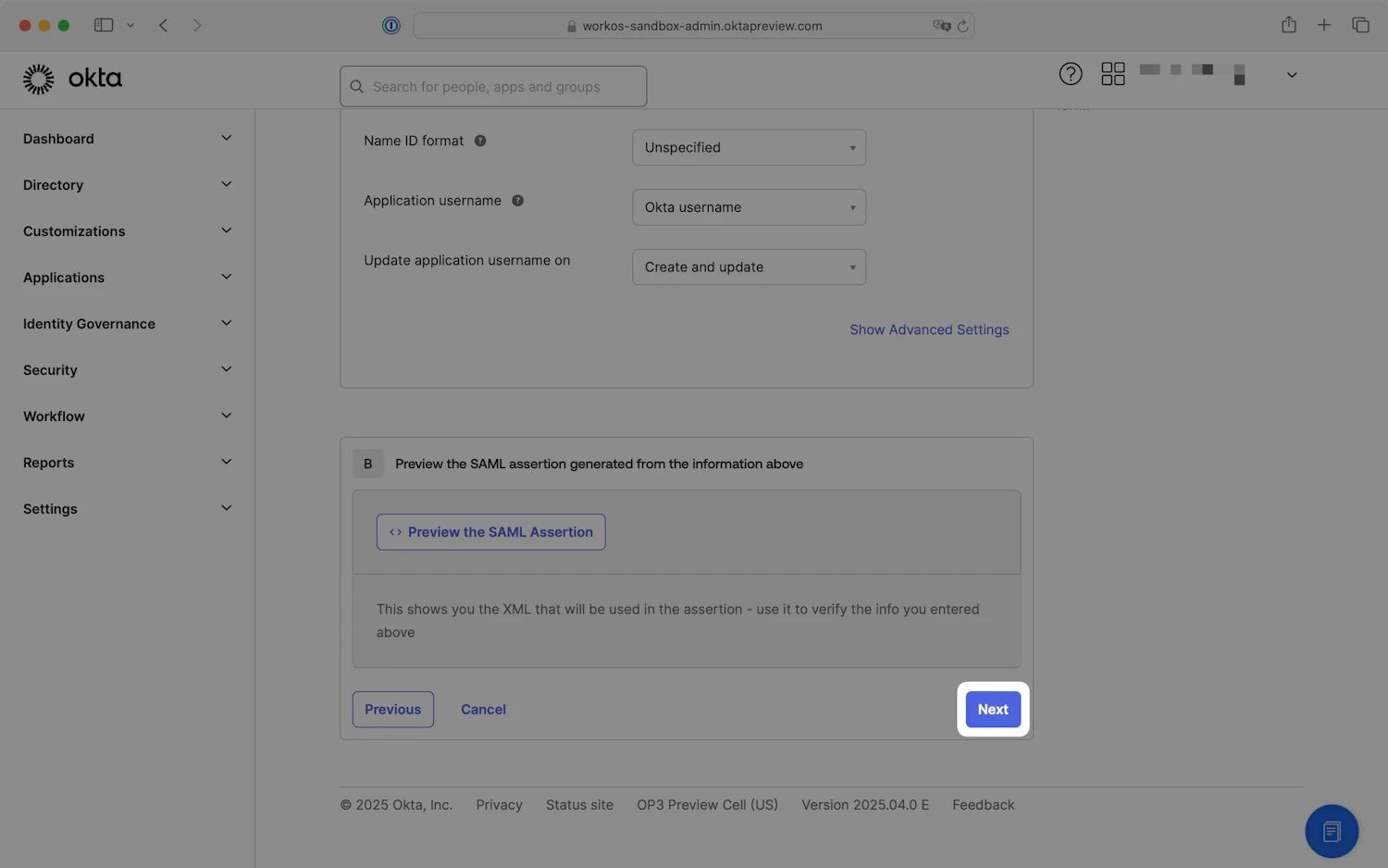
Click Next to continue - Create SAML Integration wizard
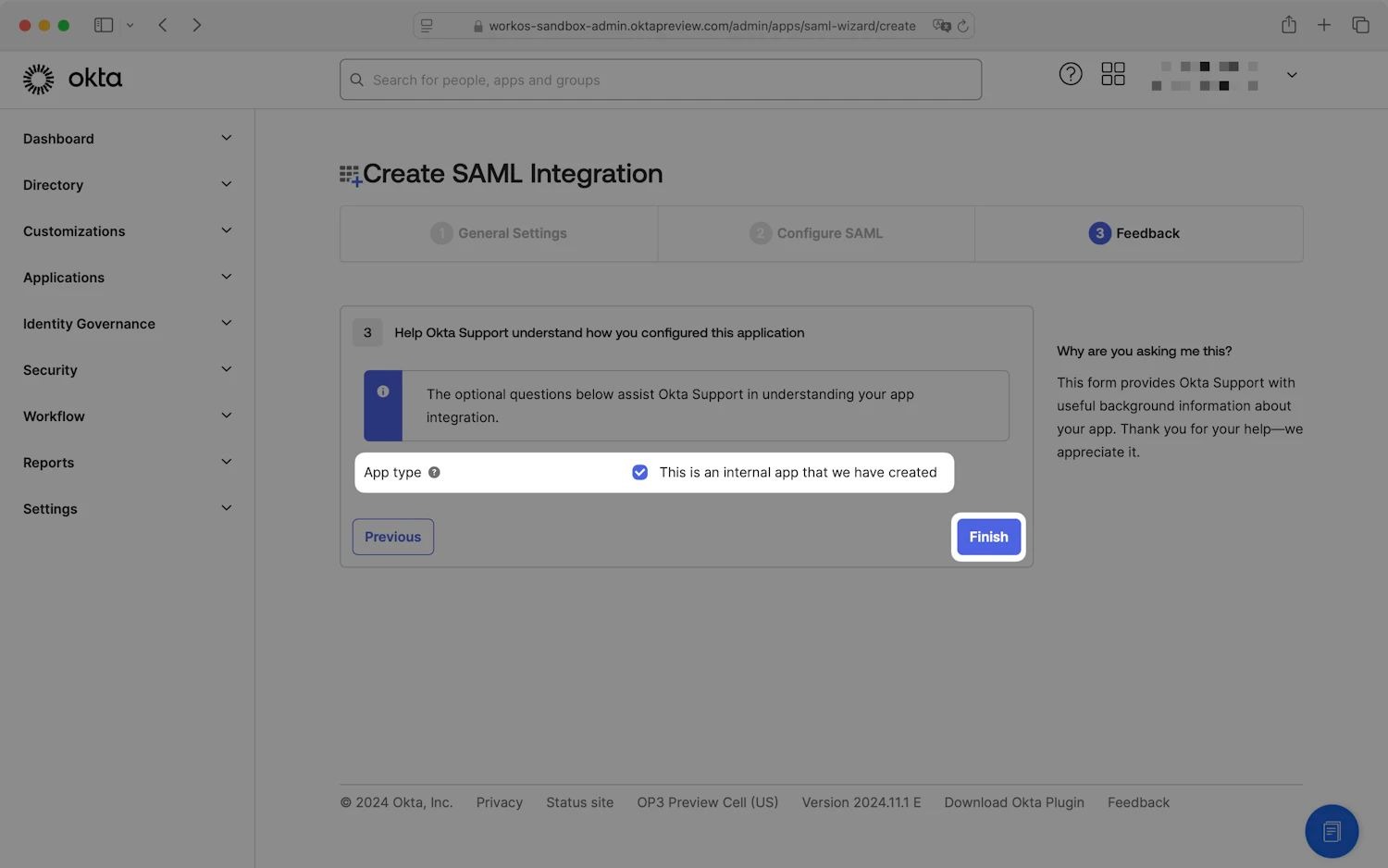
Step 4: Submit Application Feedback
On the Feedback step, check the This is an internal app that we have created option, then click Finish.
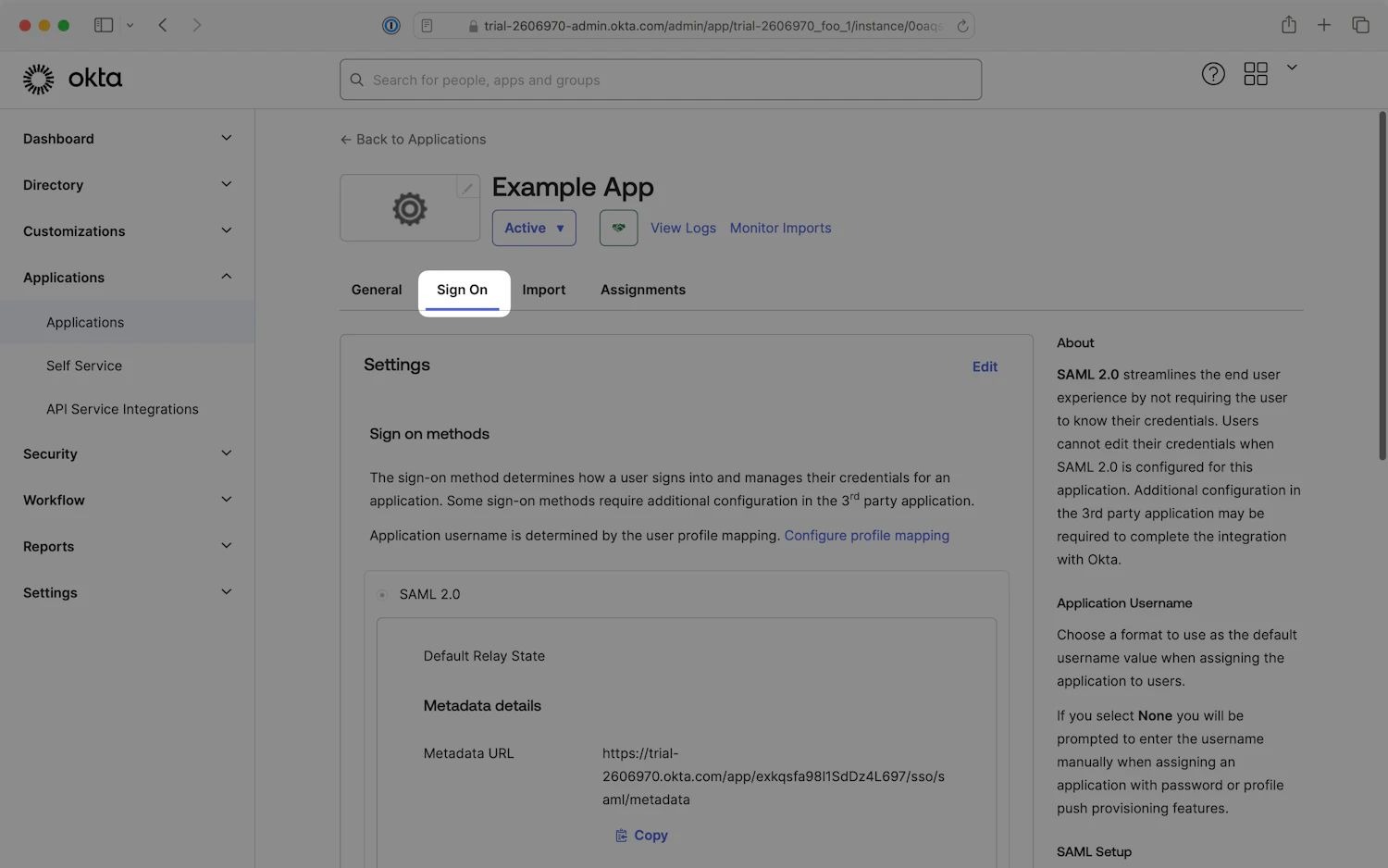
Step 5: Set Identity Provider Metadata
- Choose either
Dynamic configuration(recommended) orManual configuration(enter identity provider details). - On the Sign On tab, in the Metadata details section, locate the Metadata URL and click on the
Copybutton.
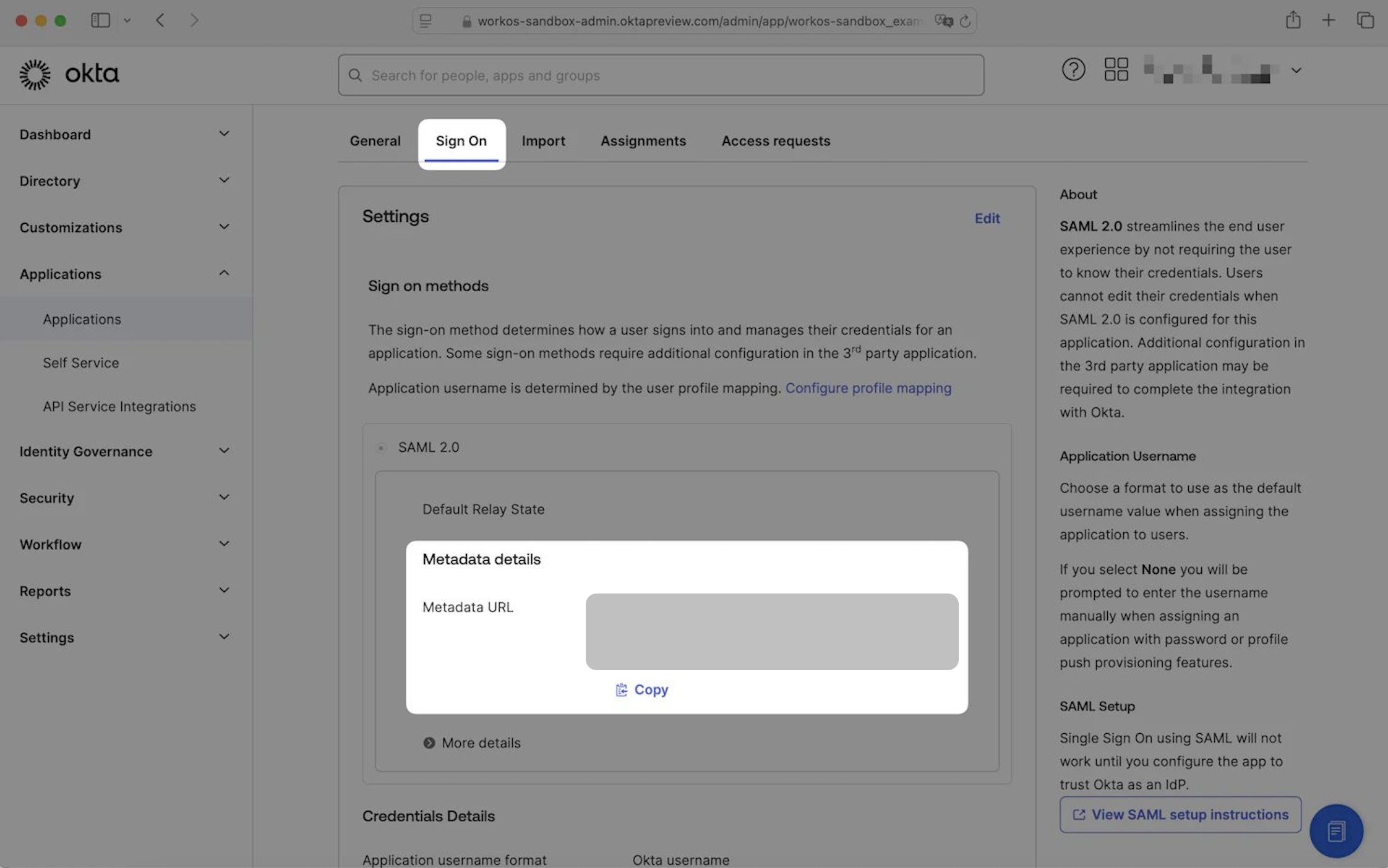
Metadata details - Set Identity Provider Metadata
- Paste the value into the Identity provider metadata URL field in the WorkOS setup guide to continue to the next step.
Step 6: Configure SAML Attributes
Depending on which features have been enabled on your Okta instance, SAML attribute configuration can be located in different areas of the Okta admin console.
- On the application settings page, ensure that the _Sign On _tab is selected.
Sign On tab - Application settings
- Scroll down to the SAML Attributes section and click
Edit.
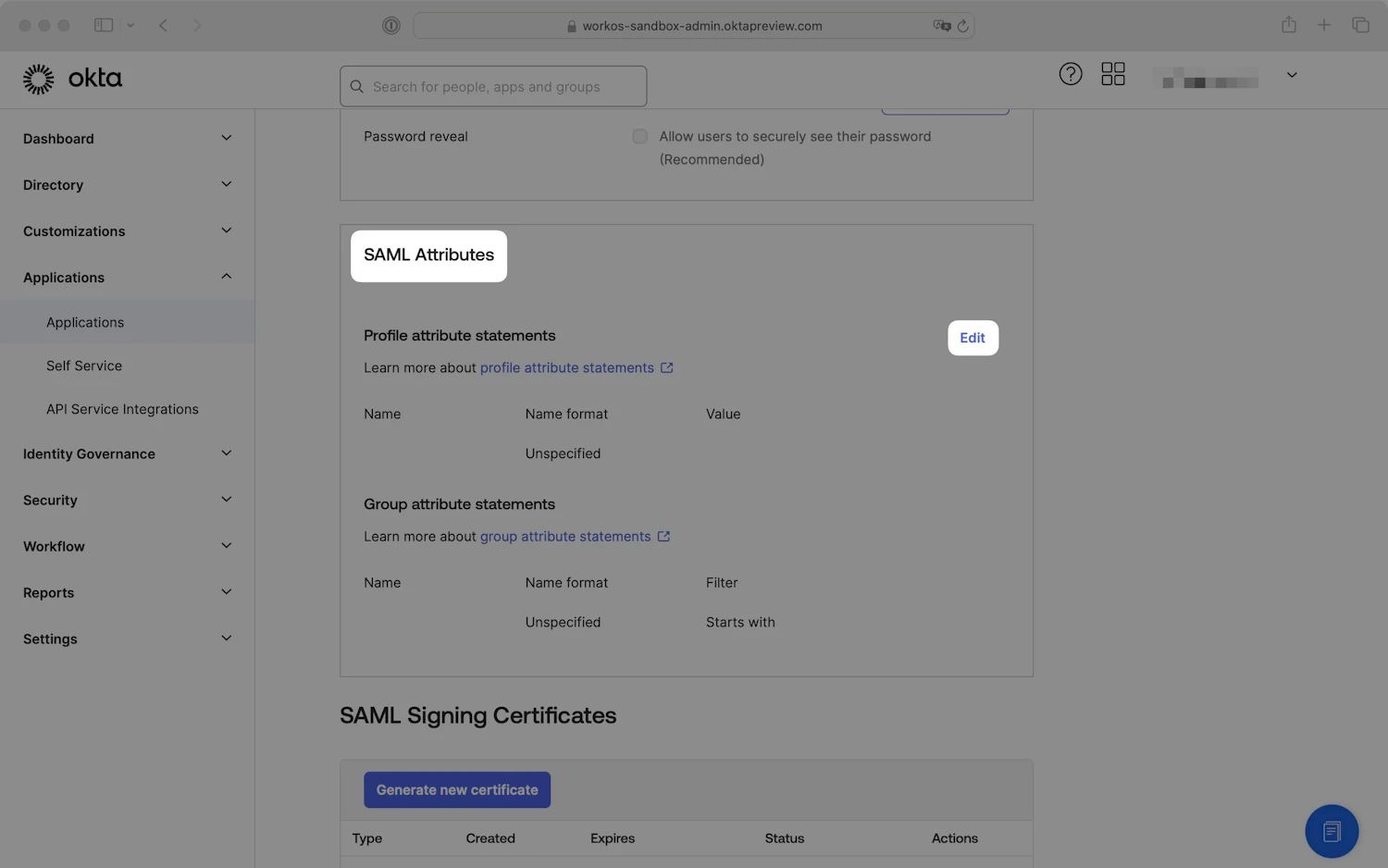
SAML Attributes - Application settings
- Add the attribute statements listed below. The name format can be left unspecified.
| Name | Value |
|---|---|
| id (Required) | user.id |
| email (Required) | user.email |
| firstName (Required) | user.firstName |
| lastName (Required) | user.lastName |
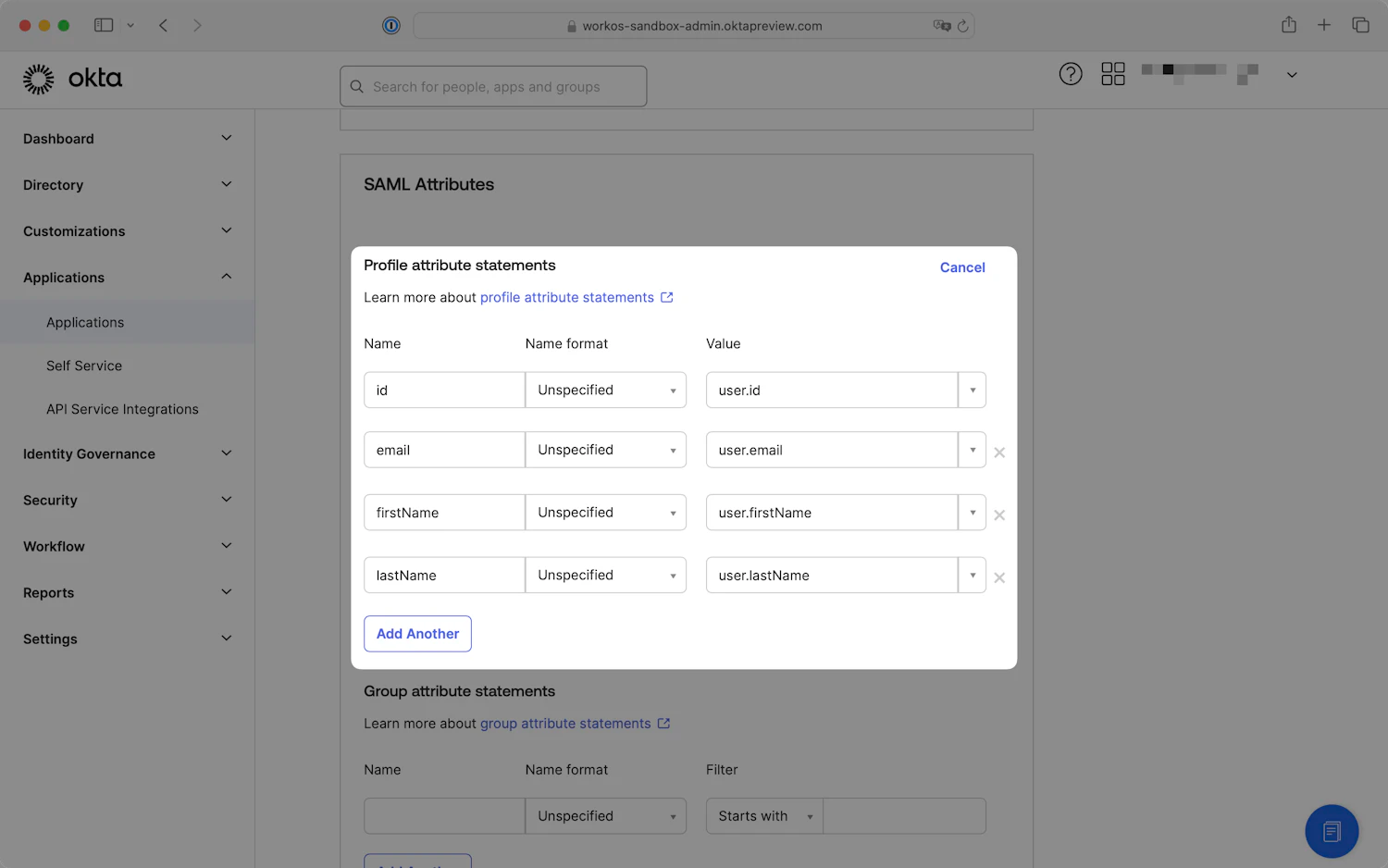
Profile attribute statements - Application settings
- Click
Next, then on the final step of the wizard, clickFinish.
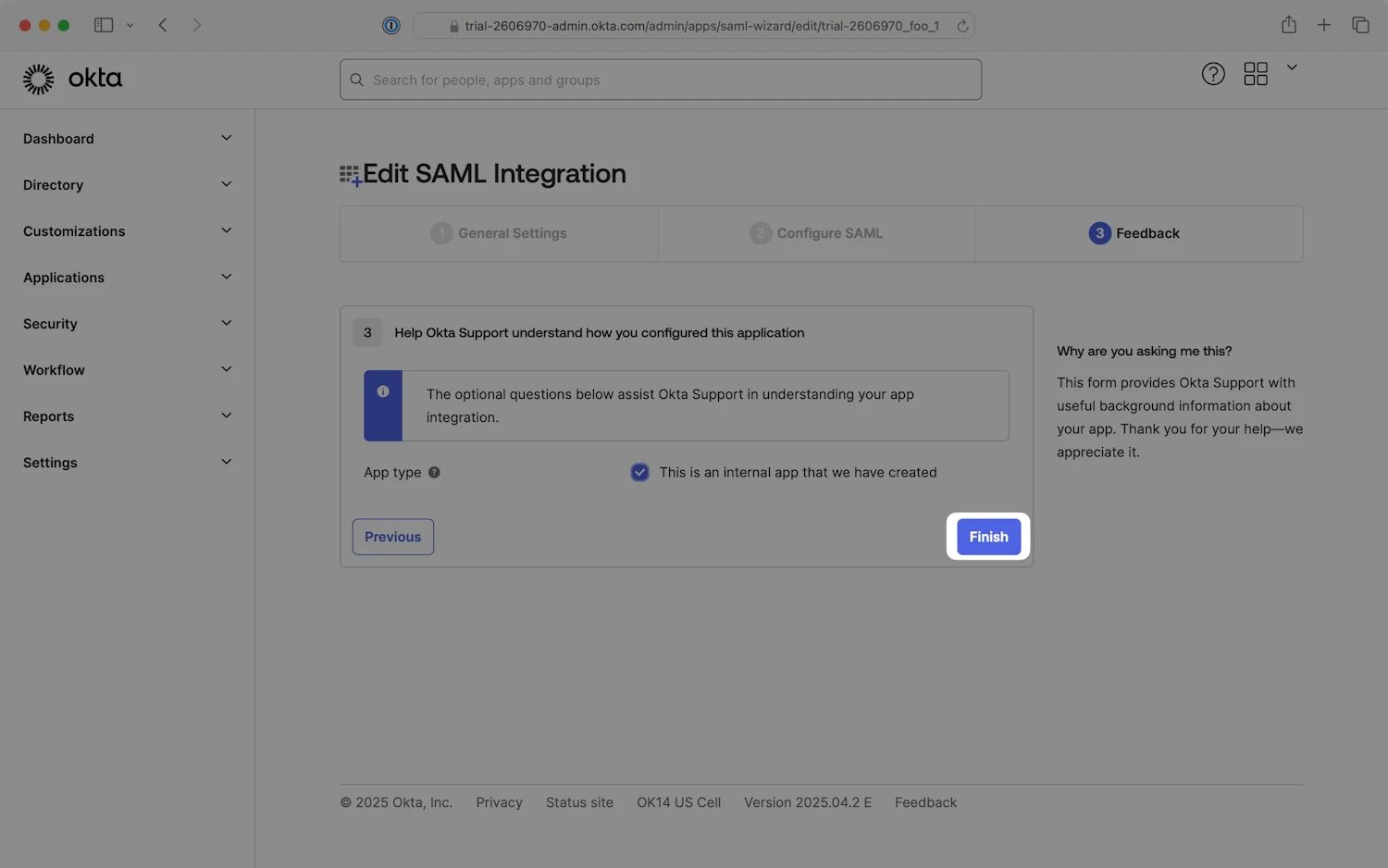
Finish editing SAML Integration
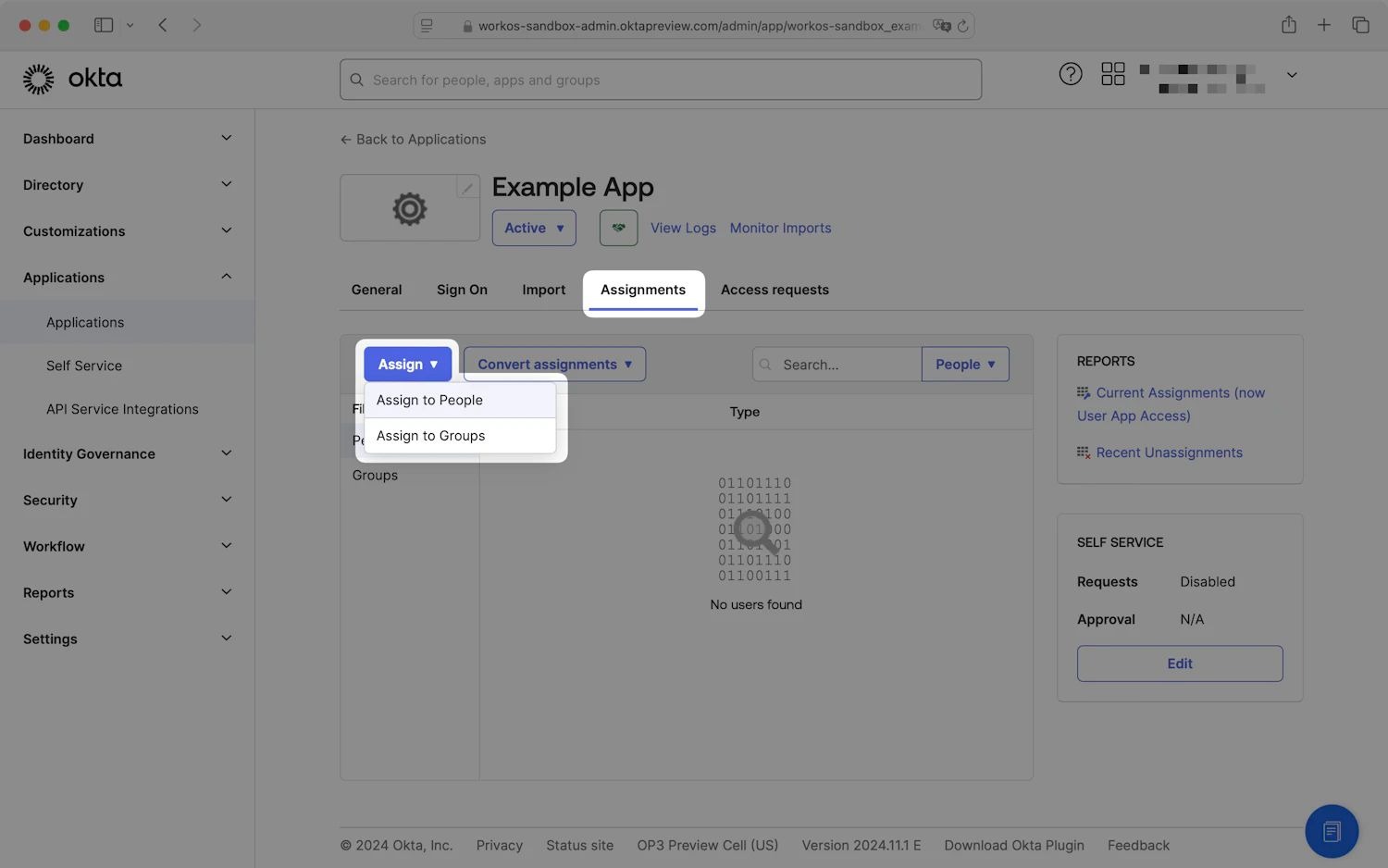
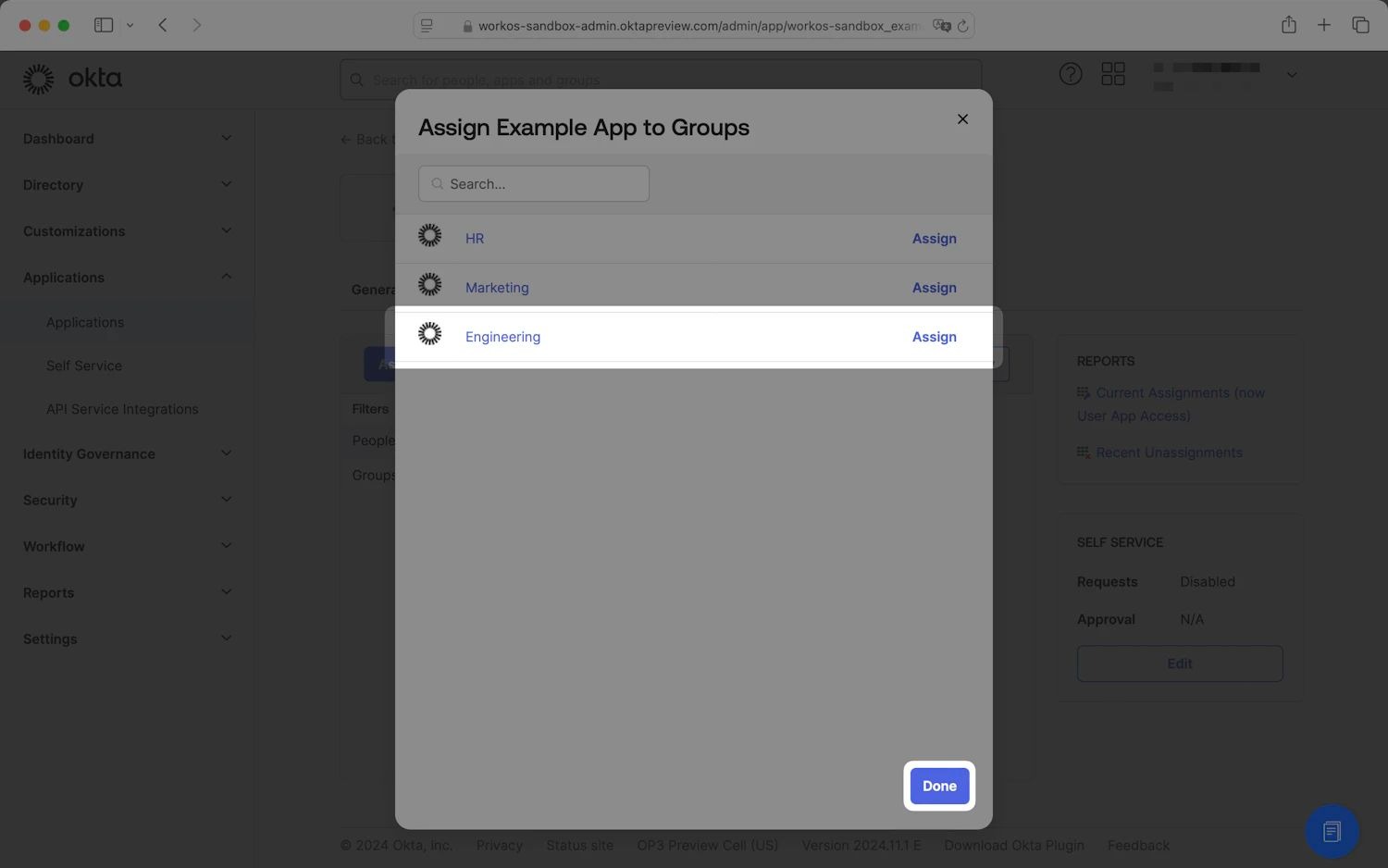
Step 7: Assign Groups to the SAML App
- On the application settings page, select the Assignments tab.
- Click
Assignand selectAssign to Groups.
- Assign the appropriate groups to the application. When you are finished, click
Done.
Step 8: Test Single Sign-On
Test configure a connection to Okta via SAML.signing in with Okta at the last stage of the WorkOS guide to verify that the single sign-on connection was configured correctly.
When you finish the setup, you should get the SSO successful test notification, which would mean that the connection between WorkOS and your IdP was established:
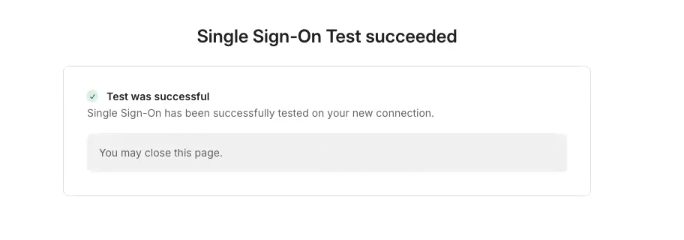
SSO Test succeeded notification
Step 9: Enforce SSO
After a successful test, please reach out to the Synthesia support team, who will send you a test login link to try accessing your account with SSO and after you confirm a successful attempt, they will be able to enforce your SSO in production.
Be sure to include:
- A validation that the tests worked
- A list of domain names managed by your IdP (e.g. synthesia.io)
Updated 6 months ago